Overview
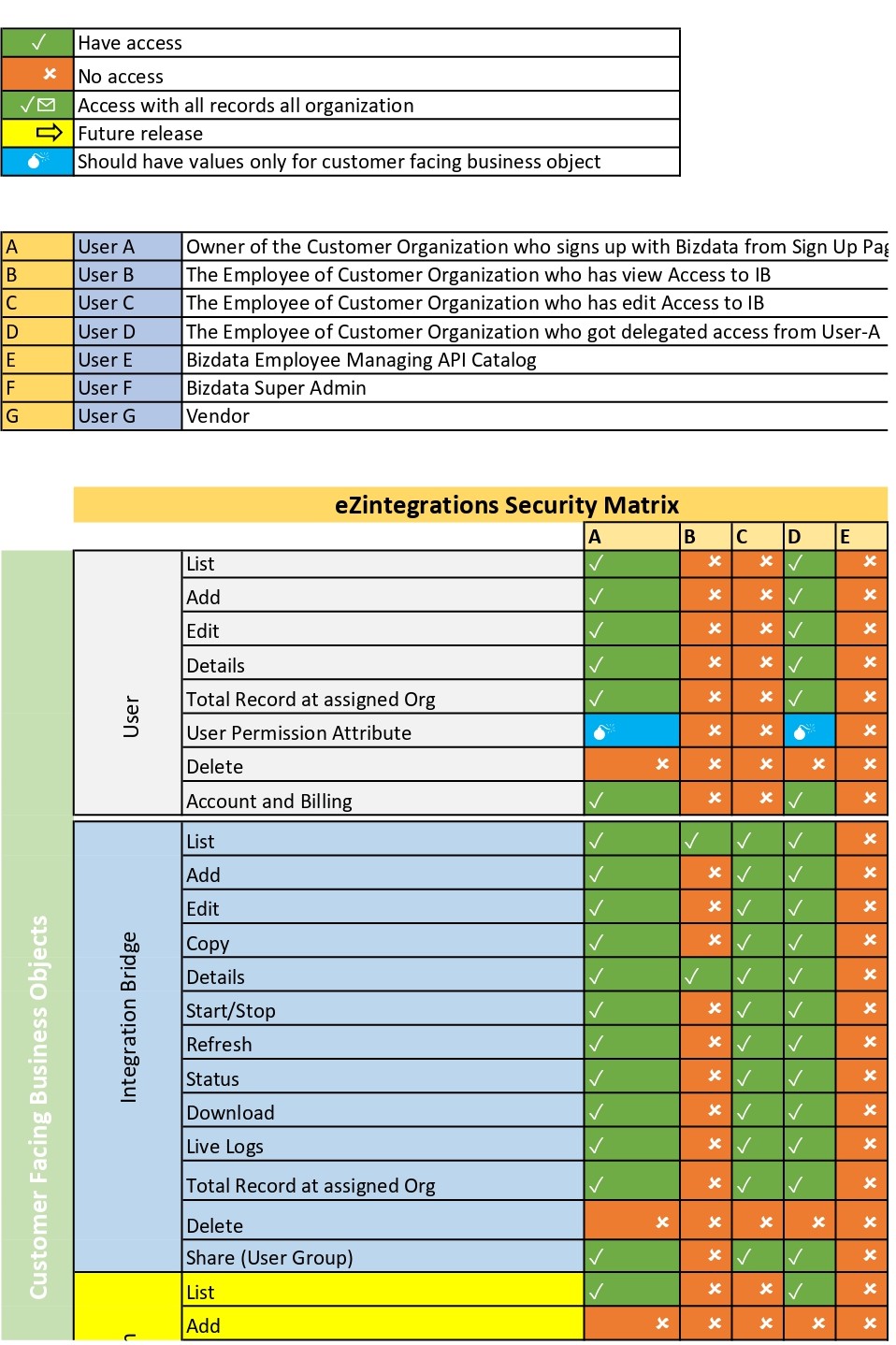
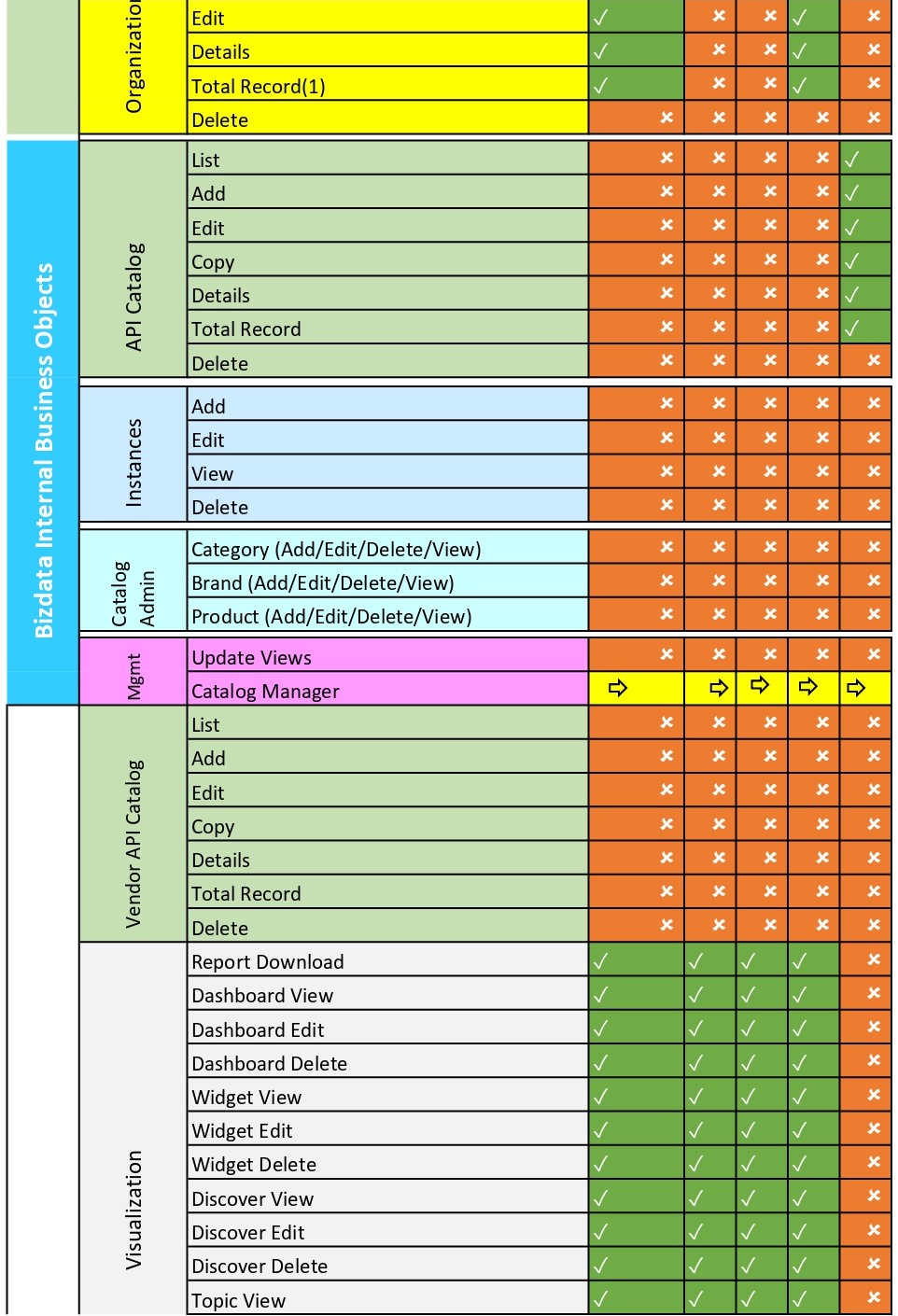
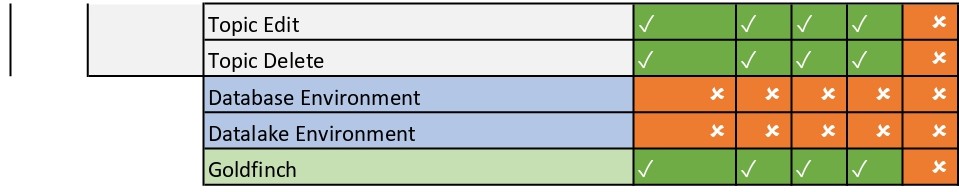
The Security Matrix provides a consolidated view of access control, permissions, and security coverage across different components of the platform. It is designed to help administrators and stakeholders understand how security is structured and enforced.
This matrix serves as a reference for reviewing permission boundaries, validating access policies, and ensuring compliance with organizational security requirements.
Security Matrix Visual Reference
The following images represent the complete Security Matrix. Review each section carefully to understand permission distribution and access scope.
::contentReference[oaicite:0]{index=0}
How to Use the Security Matrix
The Security Matrix can be used as a reference during user onboarding, role configuration, audits, and access reviews.
- Validate user and role-based permissions
- Review administrative and operational access boundaries
- Support internal and external security audits
- Ensure least-privilege access implementation
Notes
- The Security Matrix reflects the current permission model.
- Changes to roles or access levels should be reviewed against this matrix.
- Only authorized administrators should modify security configurations.




